Profile Management – Part 1
Hi,
Recently I had a poll on Twitter asking what my next subject should be here on the blog, and the winner was profile management. I like that subject because it lays the ground for so many things in the user experience in any work scenario containing IT, and thereby also Citrix which I spend a lot of my time on.
In this first part I will list some of the deciding points when choose type of profile and which options I will be testing in this blog series.
Profile types
First let’s have a look at what type of profiles we can choose from:
- Local
- Roaming
- Mandatory
- Hybrid
If we look at the capabilities of each type we get this (From the Citrix VDI handbook)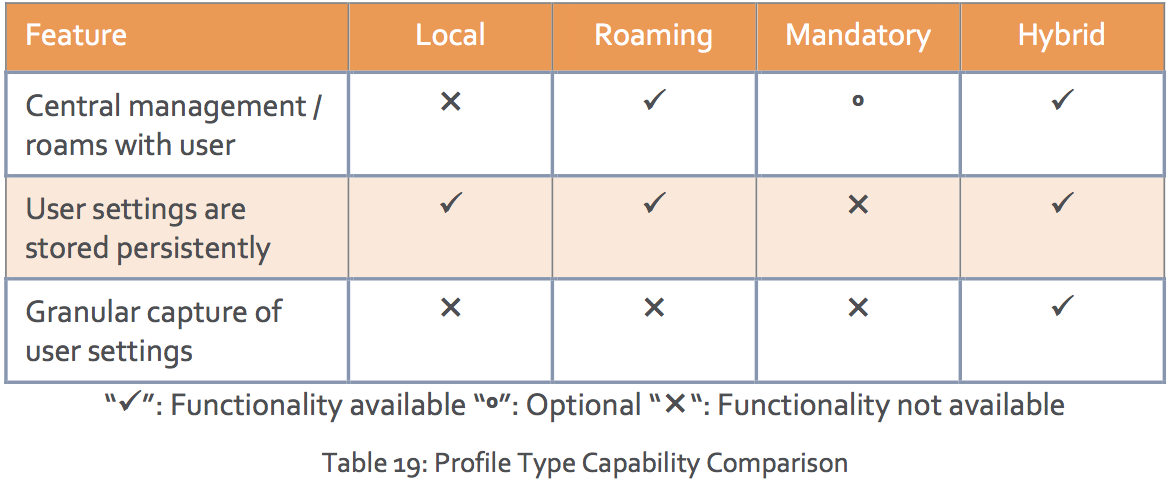 I have personally used Roaming, Mandatory and Hybrid in the Citrix deployments I have been involved in, but 99,9% for me has been either Roaming or Hybrid. If we look at what Citrix recommends using in the deployments we see out there we get this (Again from the Citrix VDI handbook)
I have personally used Roaming, Mandatory and Hybrid in the Citrix deployments I have been involved in, but 99,9% for me has been either Roaming or Hybrid. If we look at what Citrix recommends using in the deployments we see out there we get this (Again from the Citrix VDI handbook)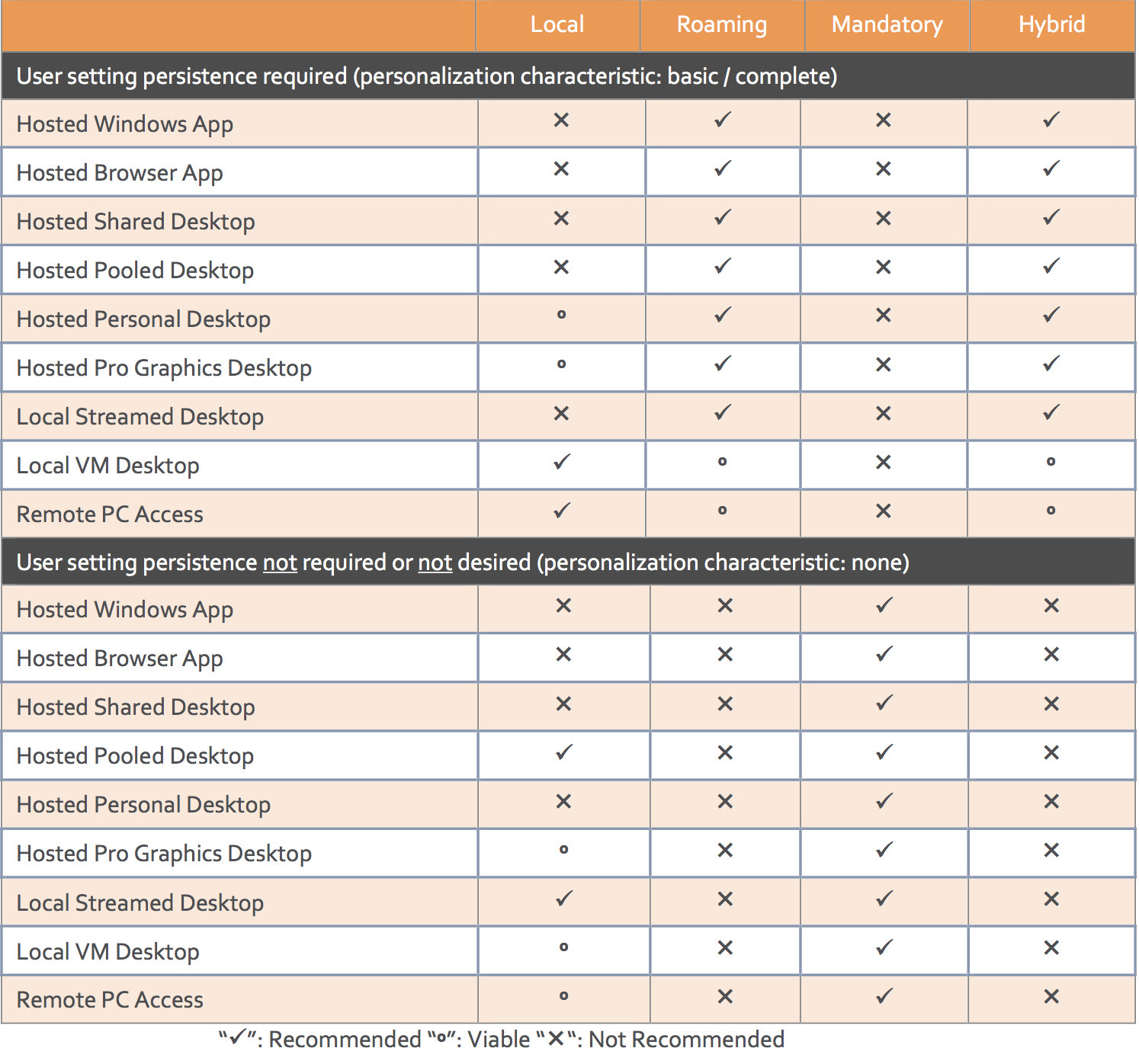 As we can see from the table above Citrix recommends roaming or hybrid profiles for almost all deployments that needs user settings persistence. This doesn’t come as a surprise since we need a consistent experience for our users. On the flip side, mandatory profiles are almost the only recommended solution for none persistent user settings.
As we can see from the table above Citrix recommends roaming or hybrid profiles for almost all deployments that needs user settings persistence. This doesn’t come as a surprise since we need a consistent experience for our users. On the flip side, mandatory profiles are almost the only recommended solution for none persistent user settings.
An example on a hybrid user profile is Citrix User Profile Management. The meaning of a hybrid profile is that you can include and exclude just about any part of the user profile based on what you need, this could be registry keys, files or folders.
Folder redirection
Another big part of the user experience and profile management is the folder redirection part. We use folder redirection to reduce the size of the profile but still have persistence in those folders. When we look at what the Citrix VDI handbook recommends in this area we get this: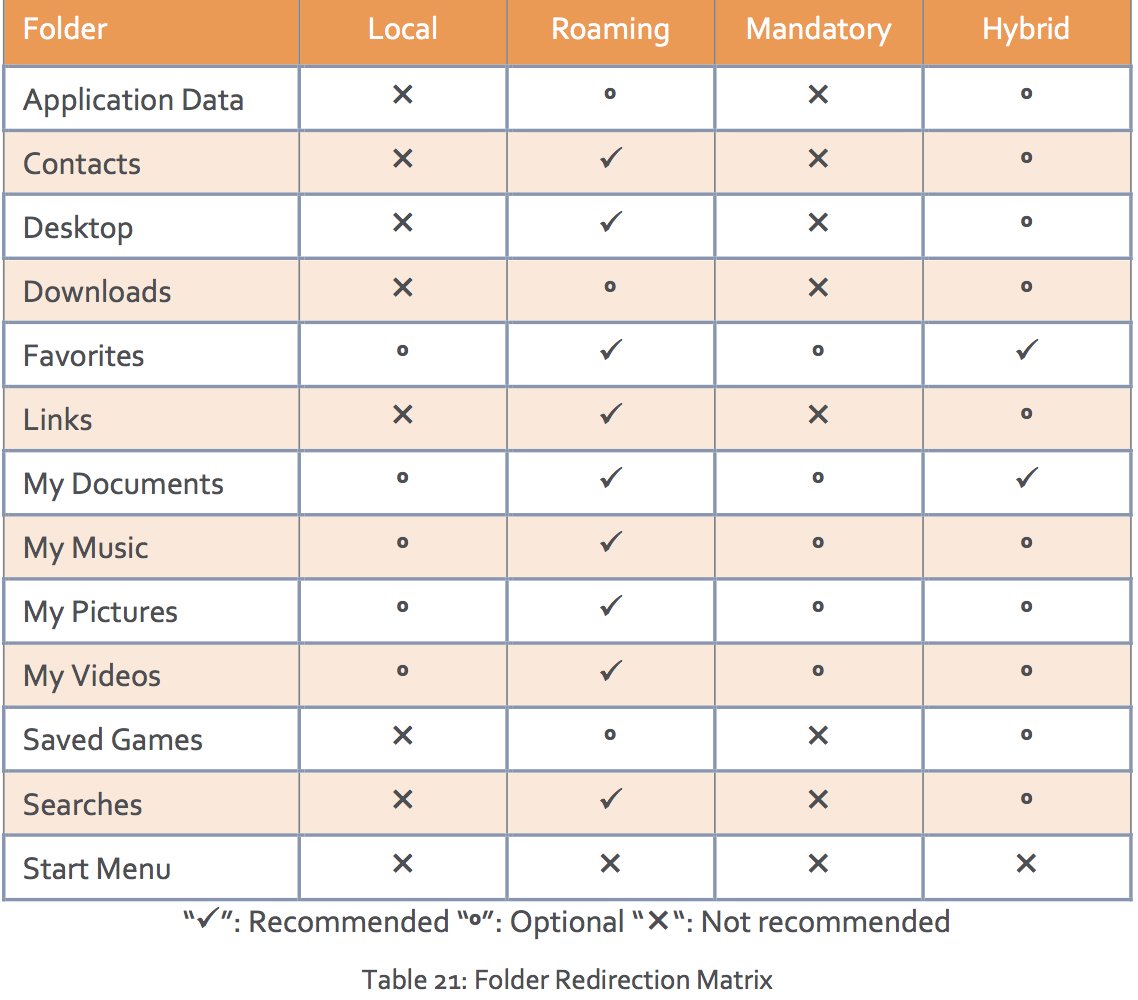 I quite often follow the recommended roaming settings for both roaming and hybrid profiles. I agree to a most of the listed from Citrix but the “Favorites” marked as recommended is something I don’t quite get. From my point of view this should be marked as an option and could often be left in the profile since in most cases we are talking about a small number of files and small size so keeping them in the profile should be fine. Another point about the favorites is that it seems that every time you write a letter in the URL bar in internet explore a call will be made to the file server over the network and thereby putting a lot of load onto network and file server.
I quite often follow the recommended roaming settings for both roaming and hybrid profiles. I agree to a most of the listed from Citrix but the “Favorites” marked as recommended is something I don’t quite get. From my point of view this should be marked as an option and could often be left in the profile since in most cases we are talking about a small number of files and small size so keeping them in the profile should be fine. Another point about the favorites is that it seems that every time you write a letter in the URL bar in internet explore a call will be made to the file server over the network and thereby putting a lot of load onto network and file server.
My recommendations
My recommendations to profile management isn’t much different from a lot of others out in the community, you need to analyze, access, test and test again. My standard setup that I normally start out with looks like this:
- Roaming or hybrid profile (if FSLogix is not an option)
- Folder redirection for
- Desktop
- Downloads
- My Documents (with music, pictures, videos to follow documents)
Next part of the series will be about
The next part of this blog series will be about the products and digging a bit deeper into each of the solutions I am going to test later. The products I will be digging into is Microsoft Roaming Profiles, Citrix Profile Management and FSLogix, ironically these are all different types of profiles, but can be used for a lot of the same scenarios.
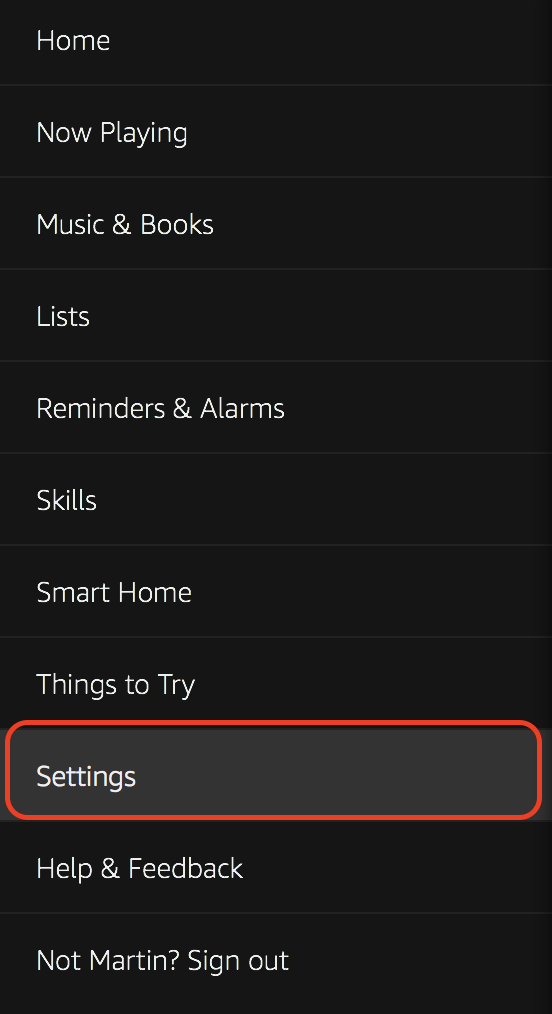
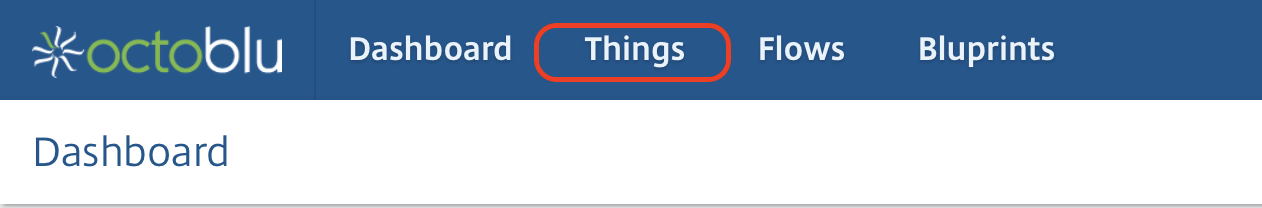
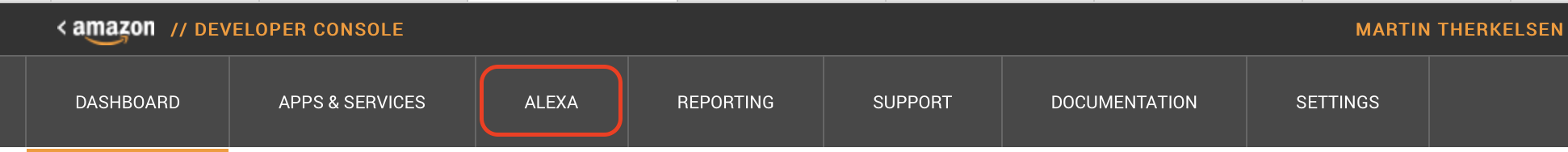
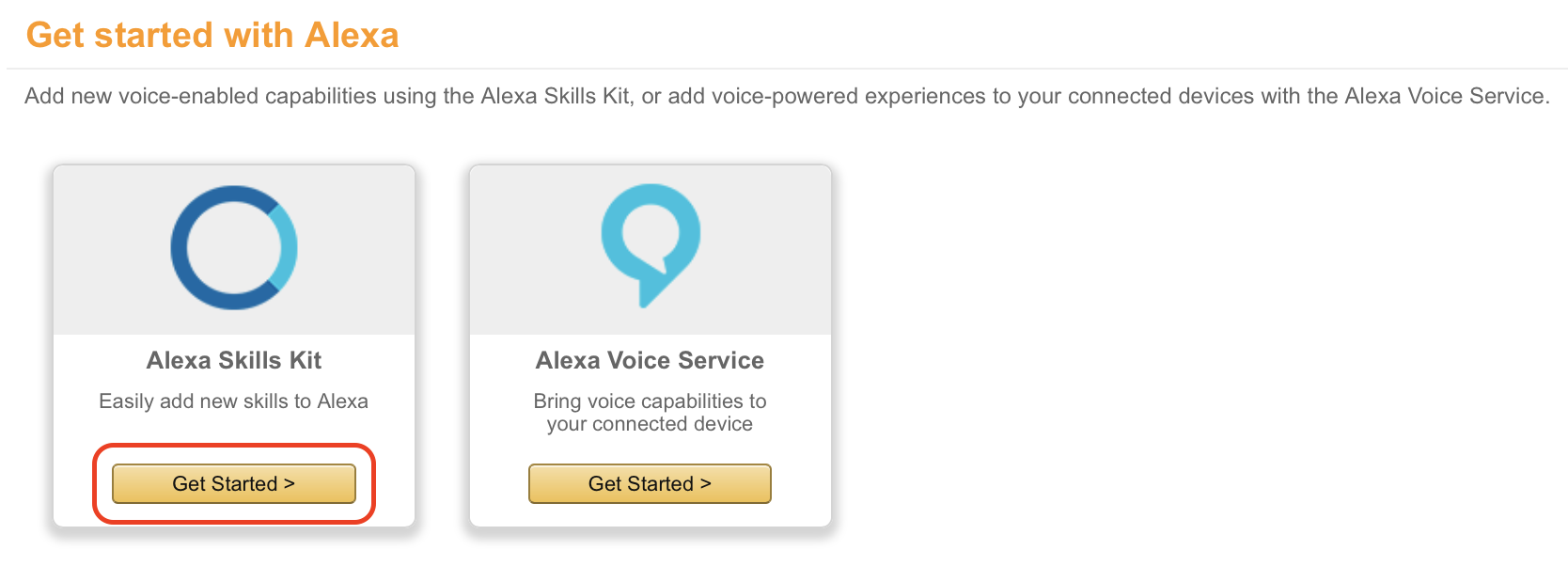
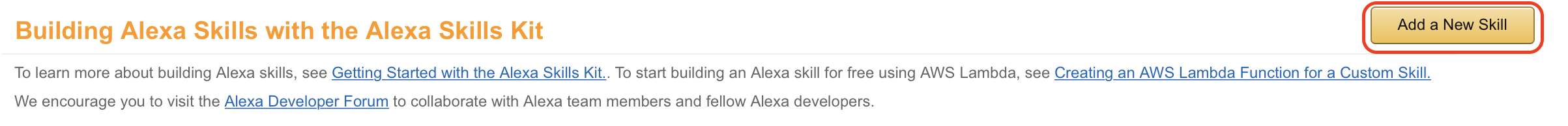
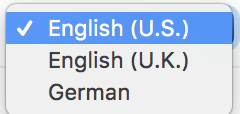
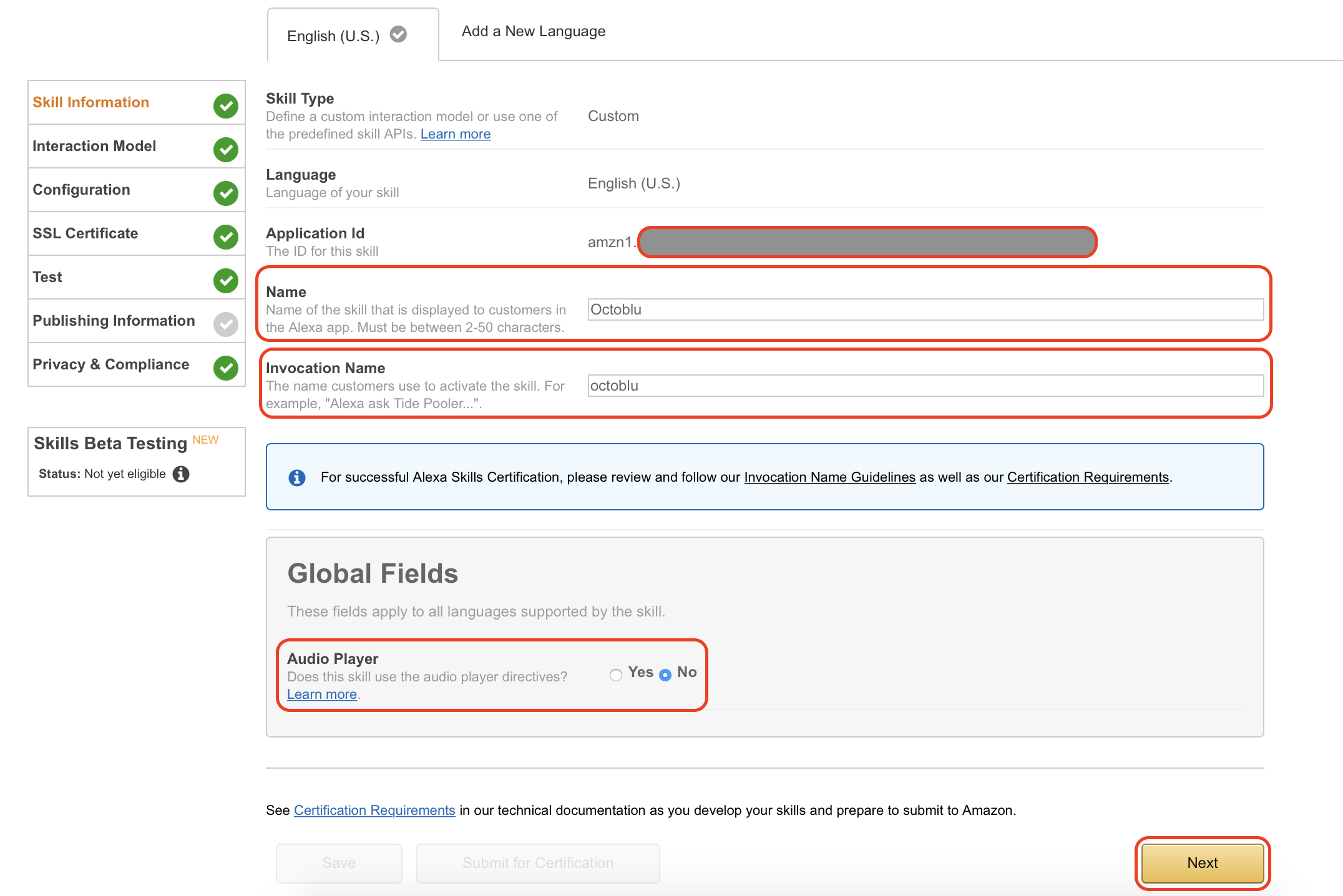
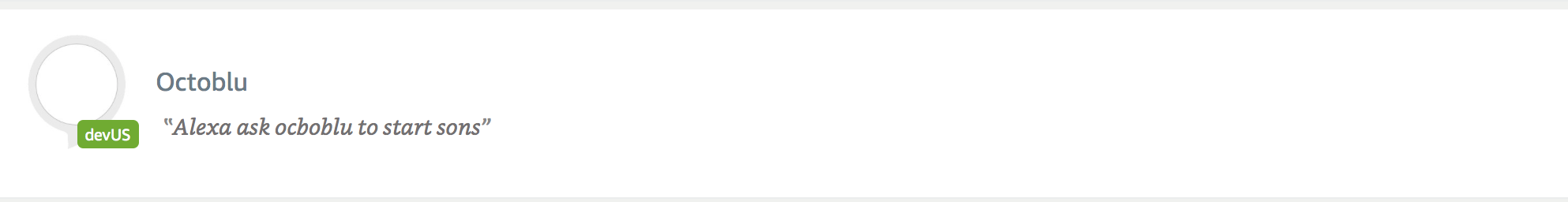
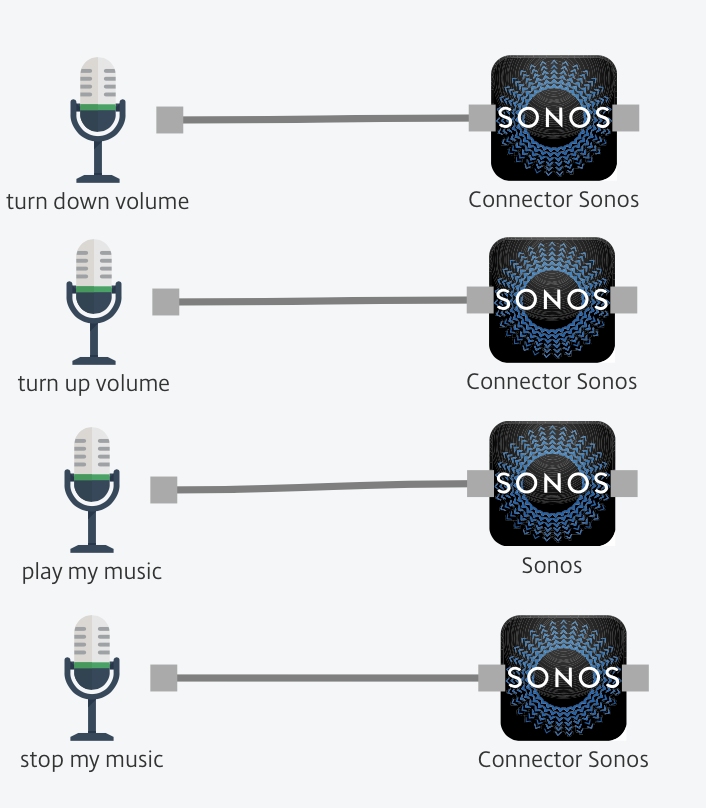
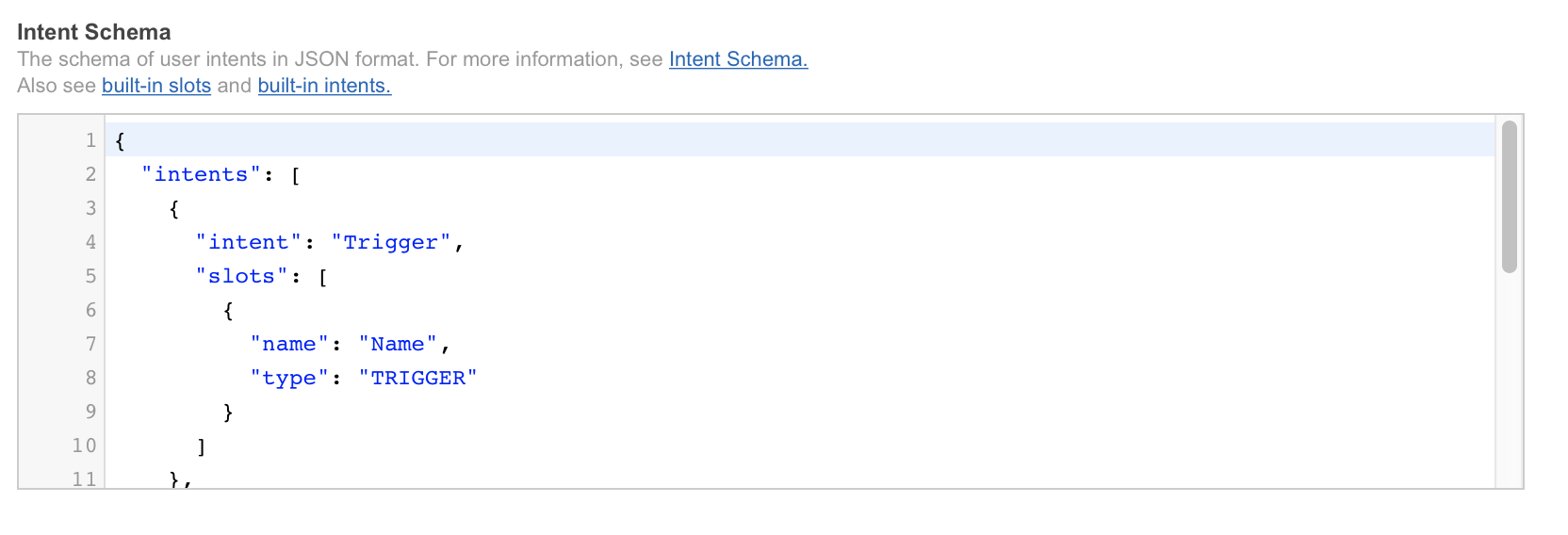 8. In the “Custom slot types” type in “TRIGGER” under “Enter Type”. “Enter Values” will be the commands Alexa and Octoblu needs to handle, in my case “play my music” and “stop my music”. When used with Alexa this will translate into “Alexa ask octoblu play my music”.
8. In the “Custom slot types” type in “TRIGGER” under “Enter Type”. “Enter Values” will be the commands Alexa and Octoblu needs to handle, in my case “play my music” and “stop my music”. When used with Alexa this will translate into “Alexa ask octoblu play my music”. 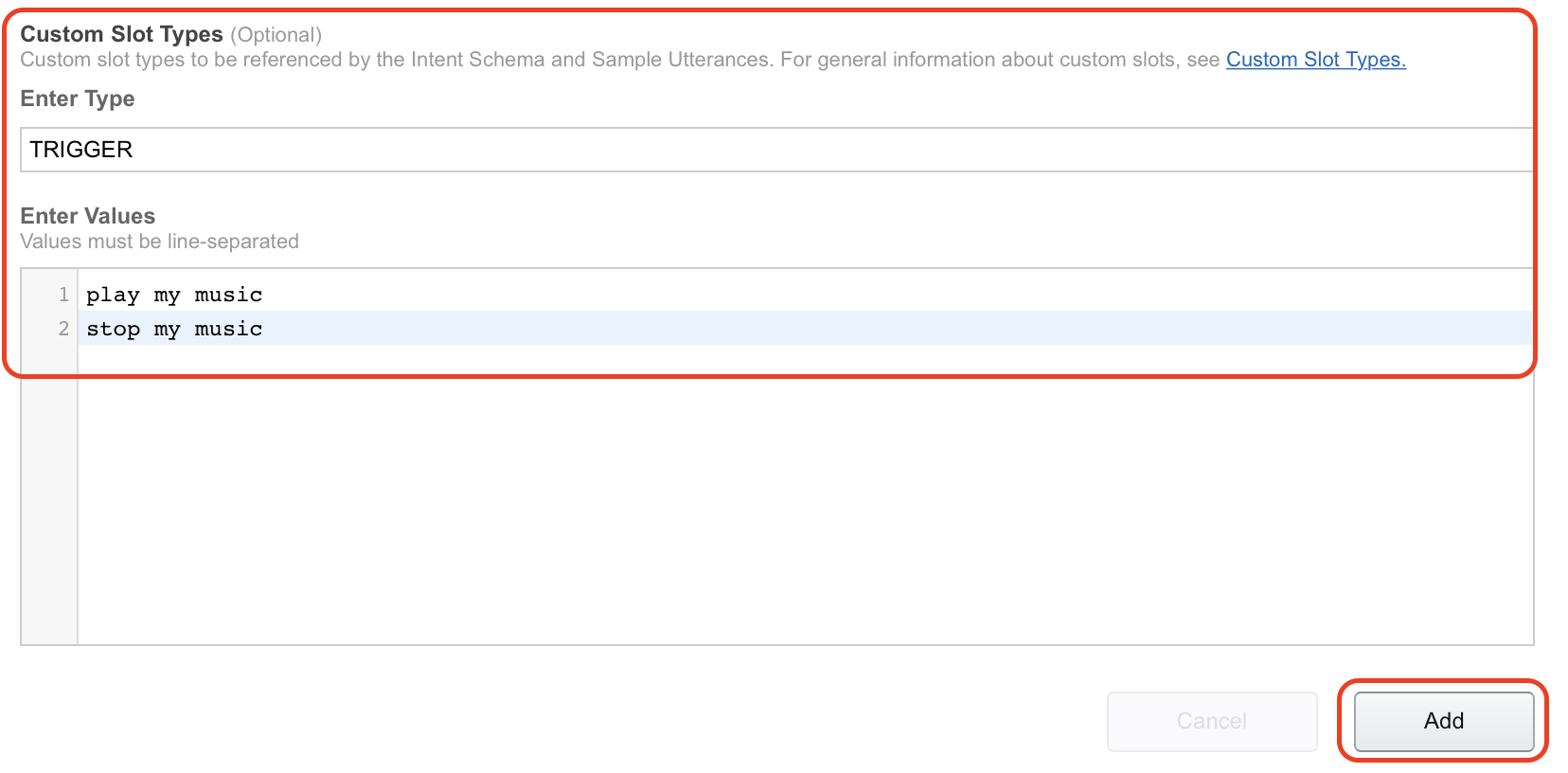 9. Under “Sample utterances” I have filled in the information from the guide as well. I have pasted both code and picture in below to illustrate.
9. Under “Sample utterances” I have filled in the information from the guide as well. I have pasted both code and picture in below to illustrate. 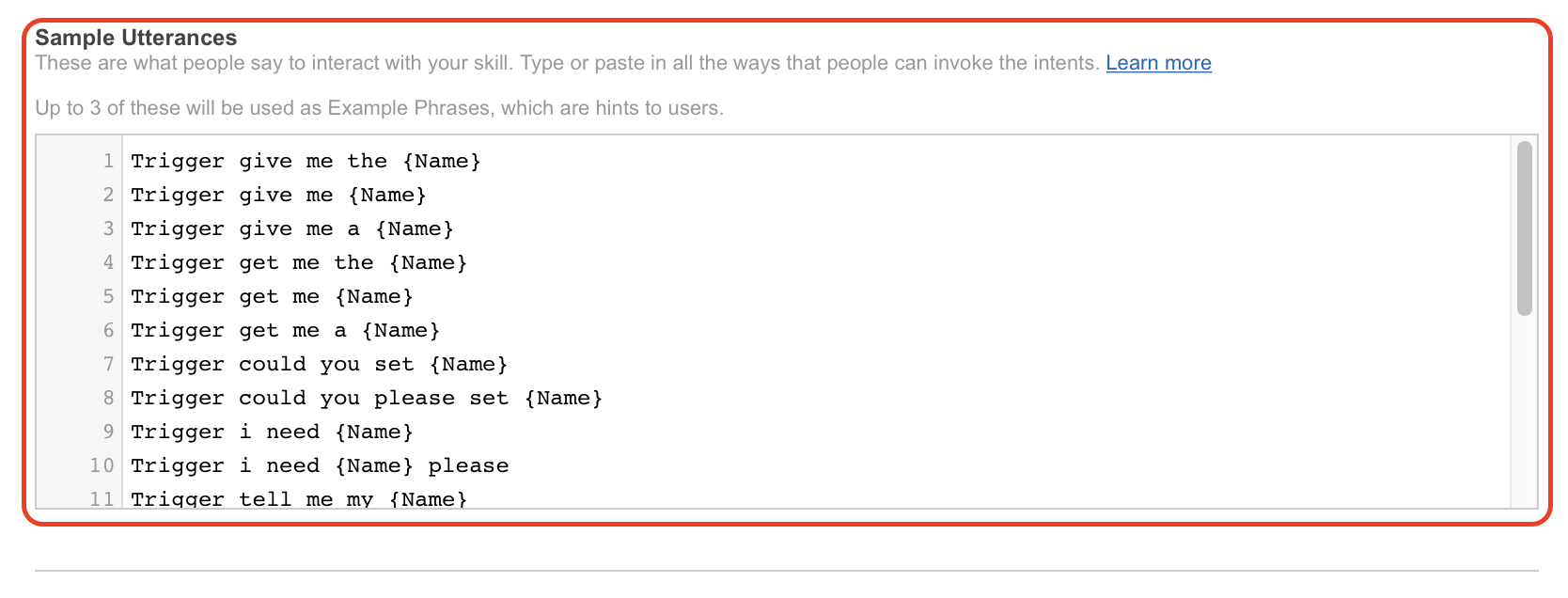 10. Click on “Next” to continue with the setup.
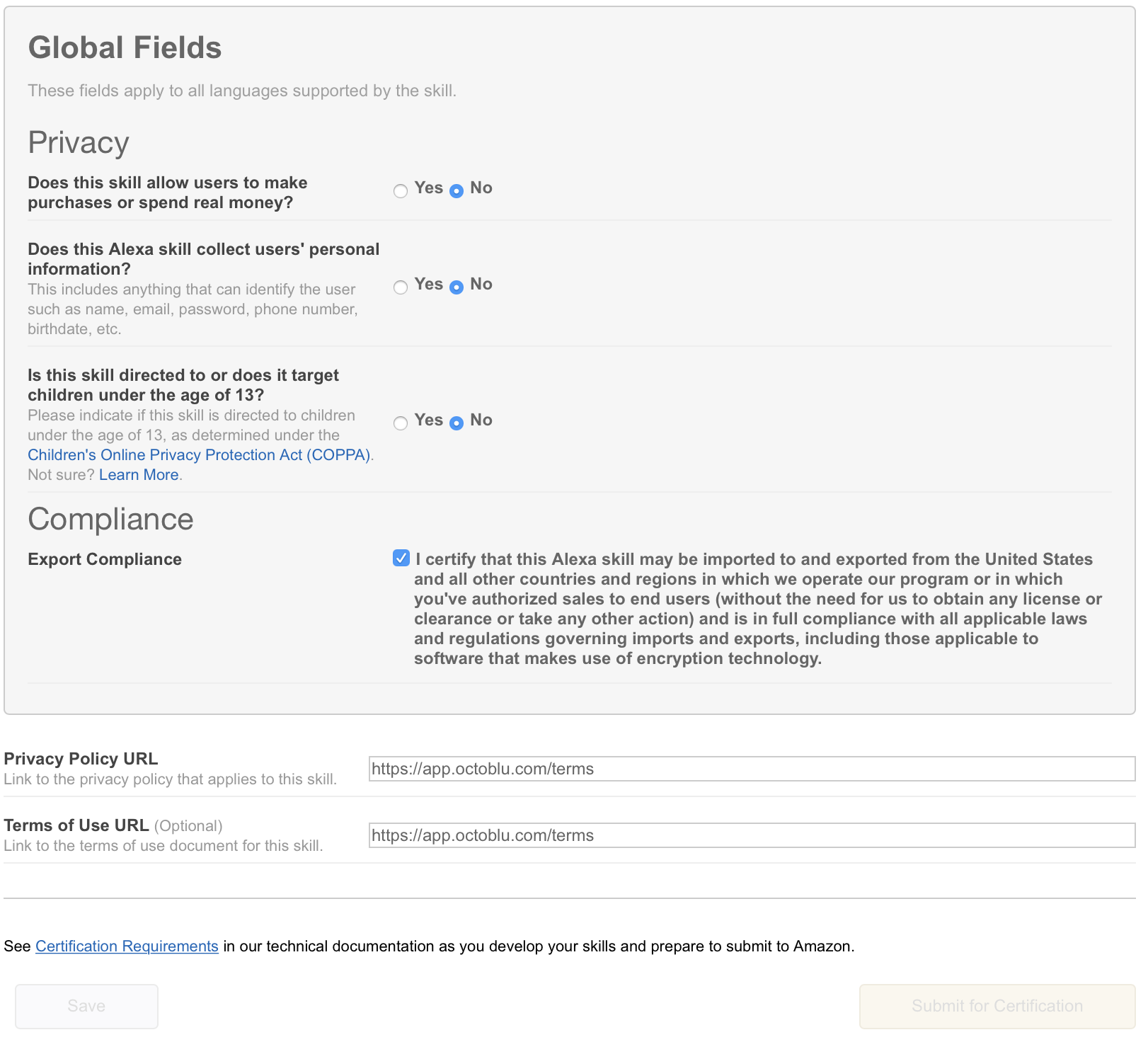
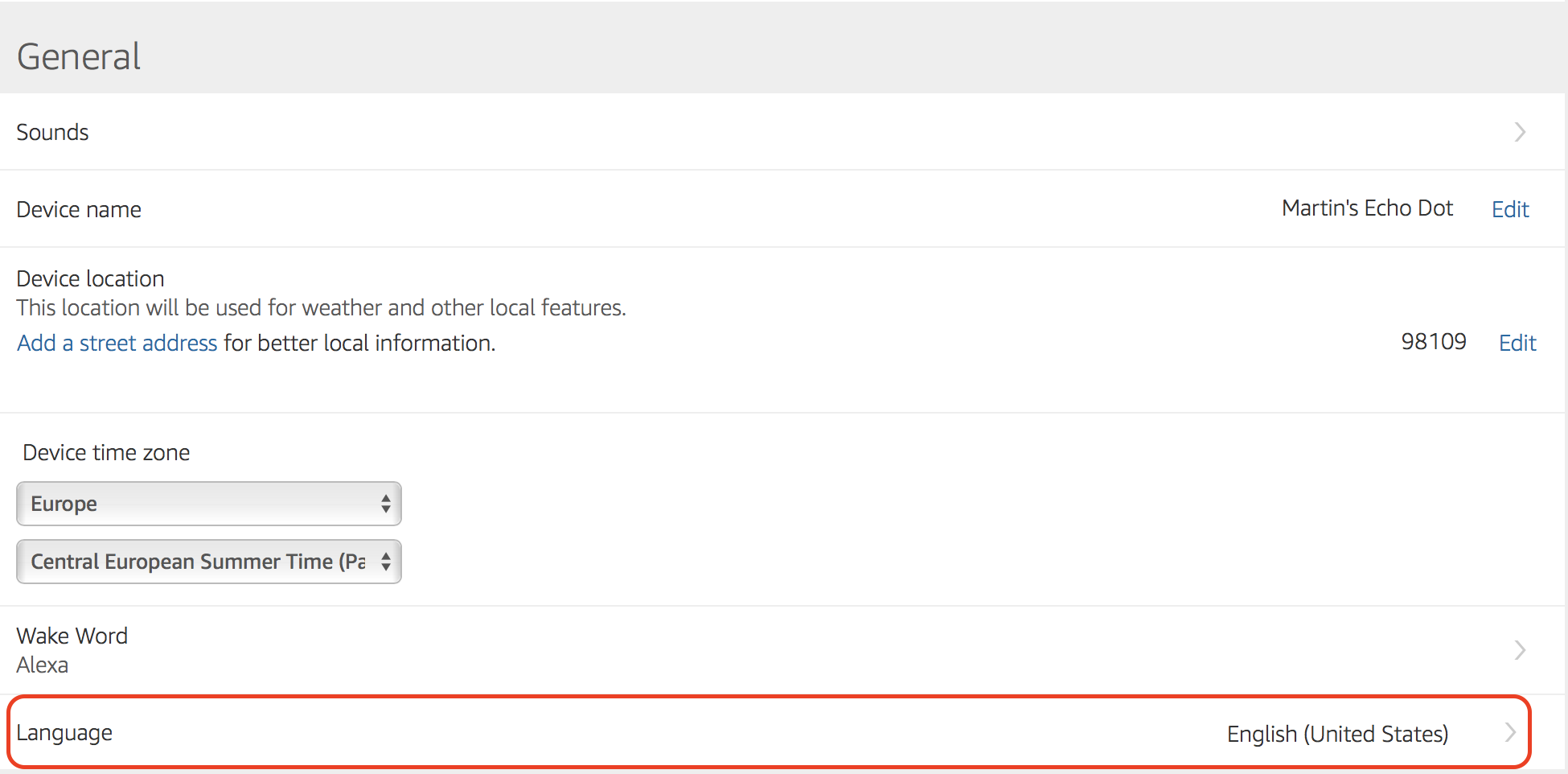
10. Click on “Next” to continue with the setup.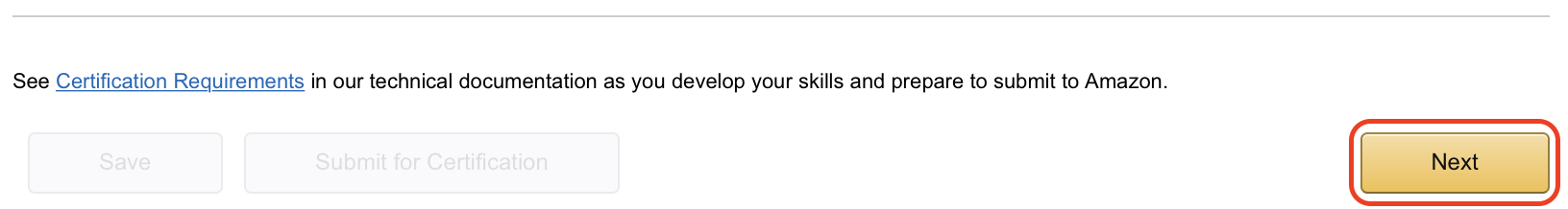 11. Under “Global Fields” mark “HTTPS” as “Service Endpoint Type” and mark the geographical location near you. I have selected “North America” this time, but will try and change that since I am based in Denmark. Also make sure that you have “Account linking” enabled by marking “Yes” in that section.
11. Under “Global Fields” mark “HTTPS” as “Service Endpoint Type” and mark the geographical location near you. I have selected “North America” this time, but will try and change that since I am based in Denmark. Also make sure that you have “Account linking” enabled by marking “Yes” in that section. 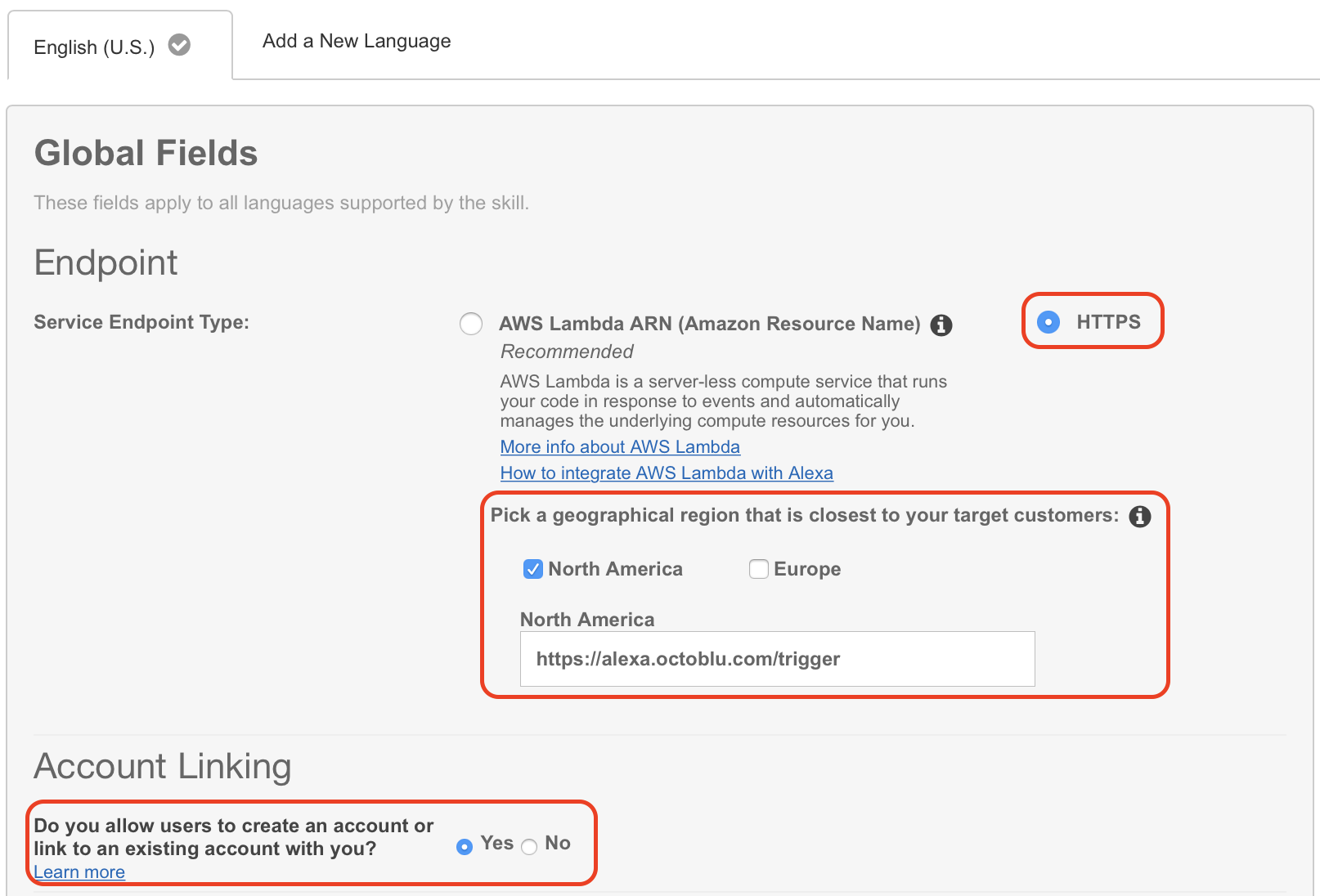 12. You will need to fill in some fields on this next screen. “Authorization URL” is “https://oauth.octoblu.com/alexa/authorize”. The client ID is the UUID from the app that we created in the Octoblu part of this guide. The domain list is a list of domains where you can fetch information from. I have used the list from the guide I found on GitHub. There is no need to set a scope for this setup.
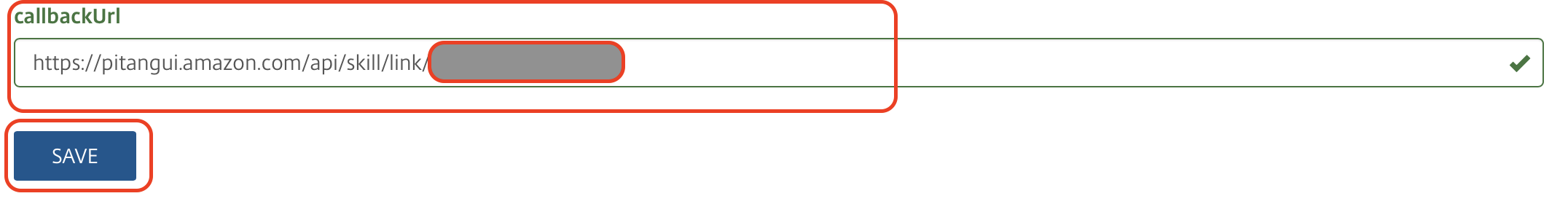
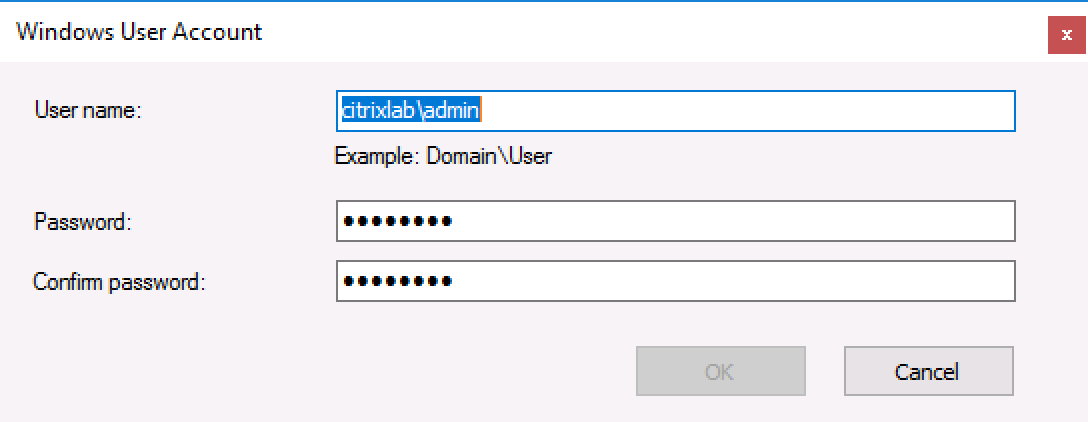
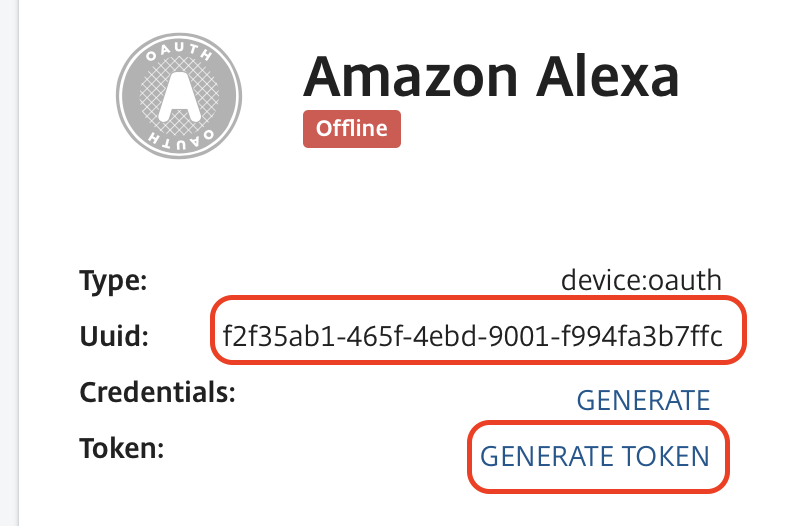
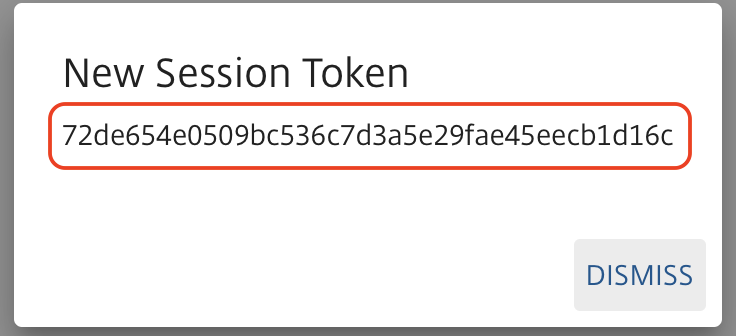
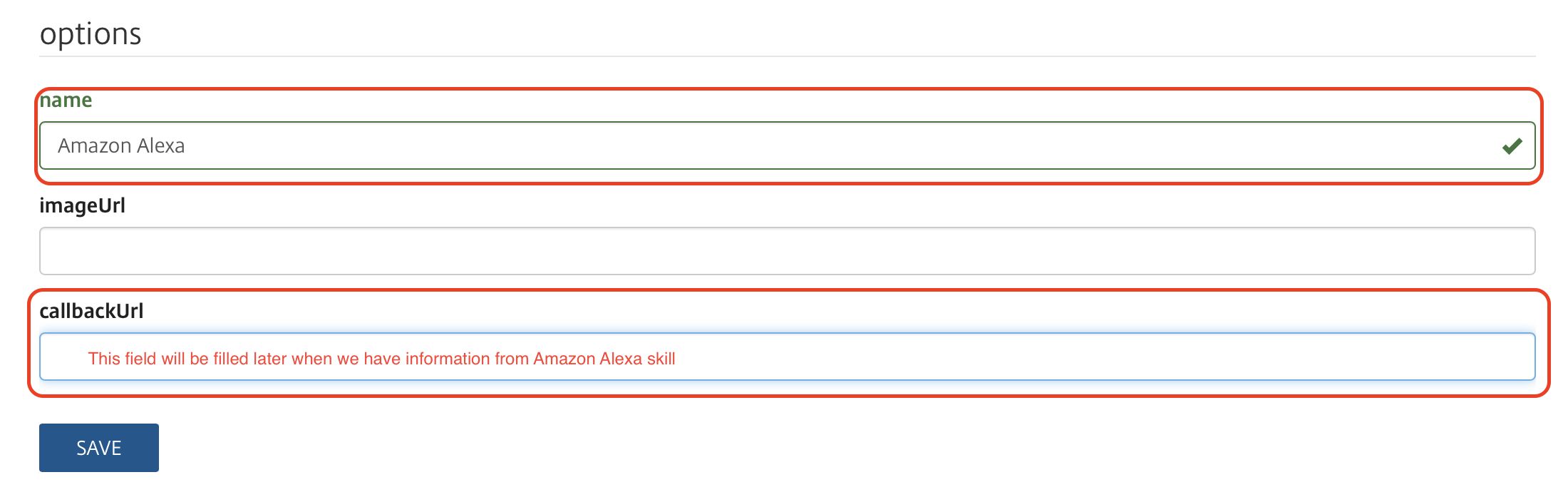
12. You will need to fill in some fields on this next screen. “Authorization URL” is “https://oauth.octoblu.com/alexa/authorize”. The client ID is the UUID from the app that we created in the Octoblu part of this guide. The domain list is a list of domains where you can fetch information from. I have used the list from the guide I found on GitHub. There is no need to set a scope for this setup. 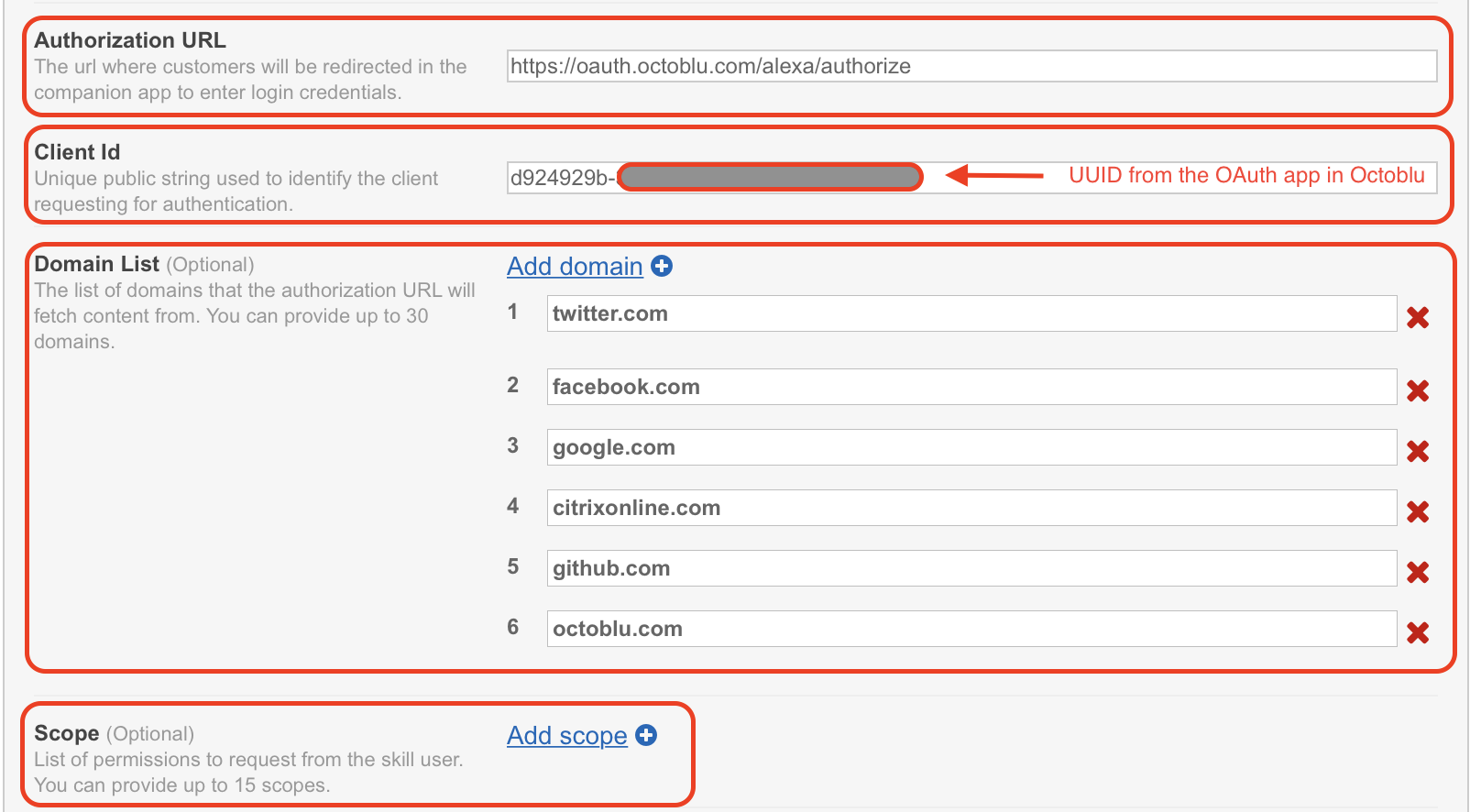 13. The redirect URLs are the ones you need to put back into the Octoblu app, so note them down. Set “Authorization grant type” to “Auth Code Grant”, set “Access Token URI” to “https://oauth.octoblu.com/access_token” and the “Client Secret” is the token that we generated in the Octoblu app. Set the “Client Authentication Scheme” to “HTTP Basic (Recommended)” and under permission I have put in “List Read” and “List Write” I don’t think they are needed, but this is how my working setup is created. The “Privacy Policy URL” I have set to “https://app.octoblu.com/terms”. Click on “Next” when ready.
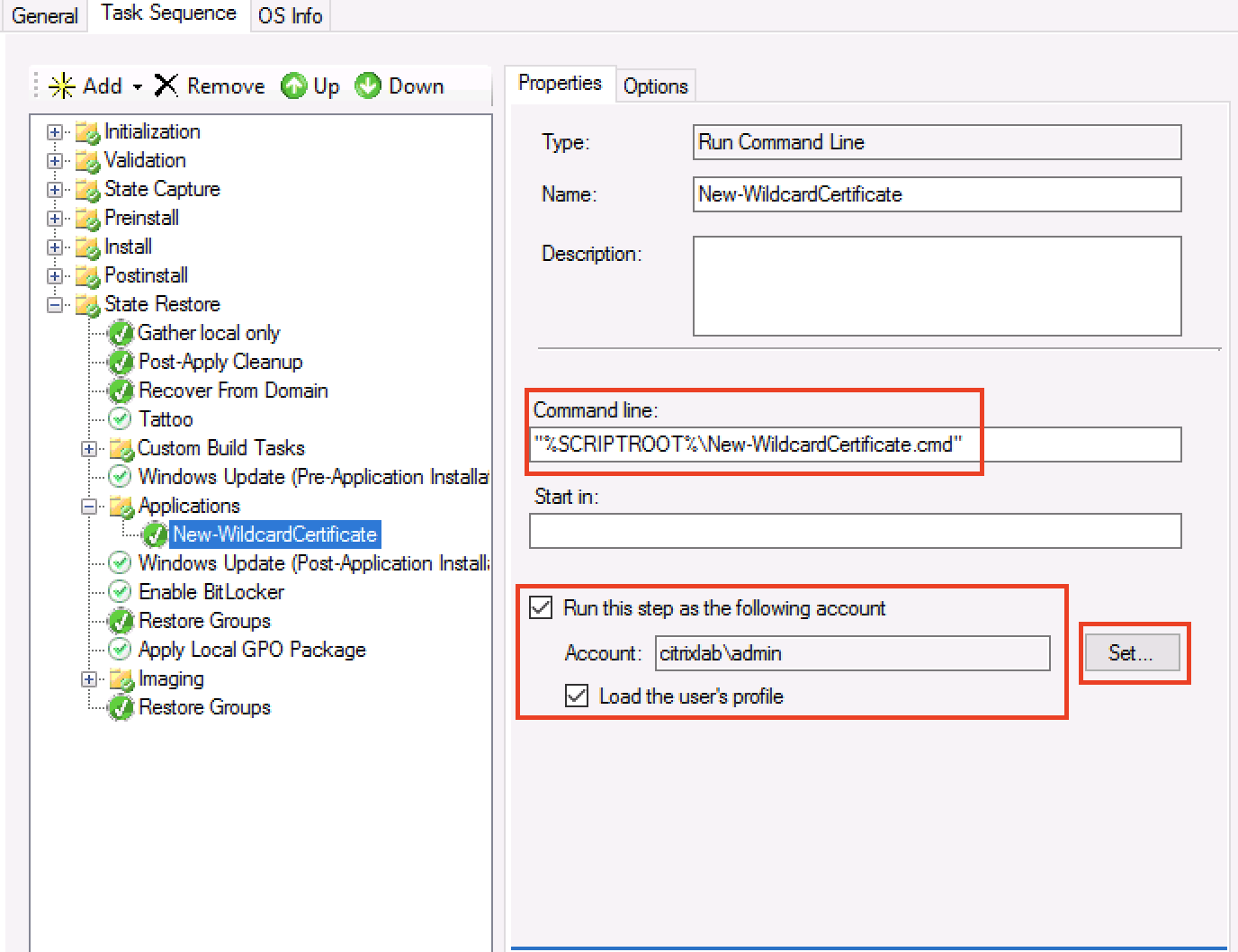
13. The redirect URLs are the ones you need to put back into the Octoblu app, so note them down. Set “Authorization grant type” to “Auth Code Grant”, set “Access Token URI” to “https://oauth.octoblu.com/access_token” and the “Client Secret” is the token that we generated in the Octoblu app. Set the “Client Authentication Scheme” to “HTTP Basic (Recommended)” and under permission I have put in “List Read” and “List Write” I don’t think they are needed, but this is how my working setup is created. The “Privacy Policy URL” I have set to “https://app.octoblu.com/terms”. Click on “Next” when ready. 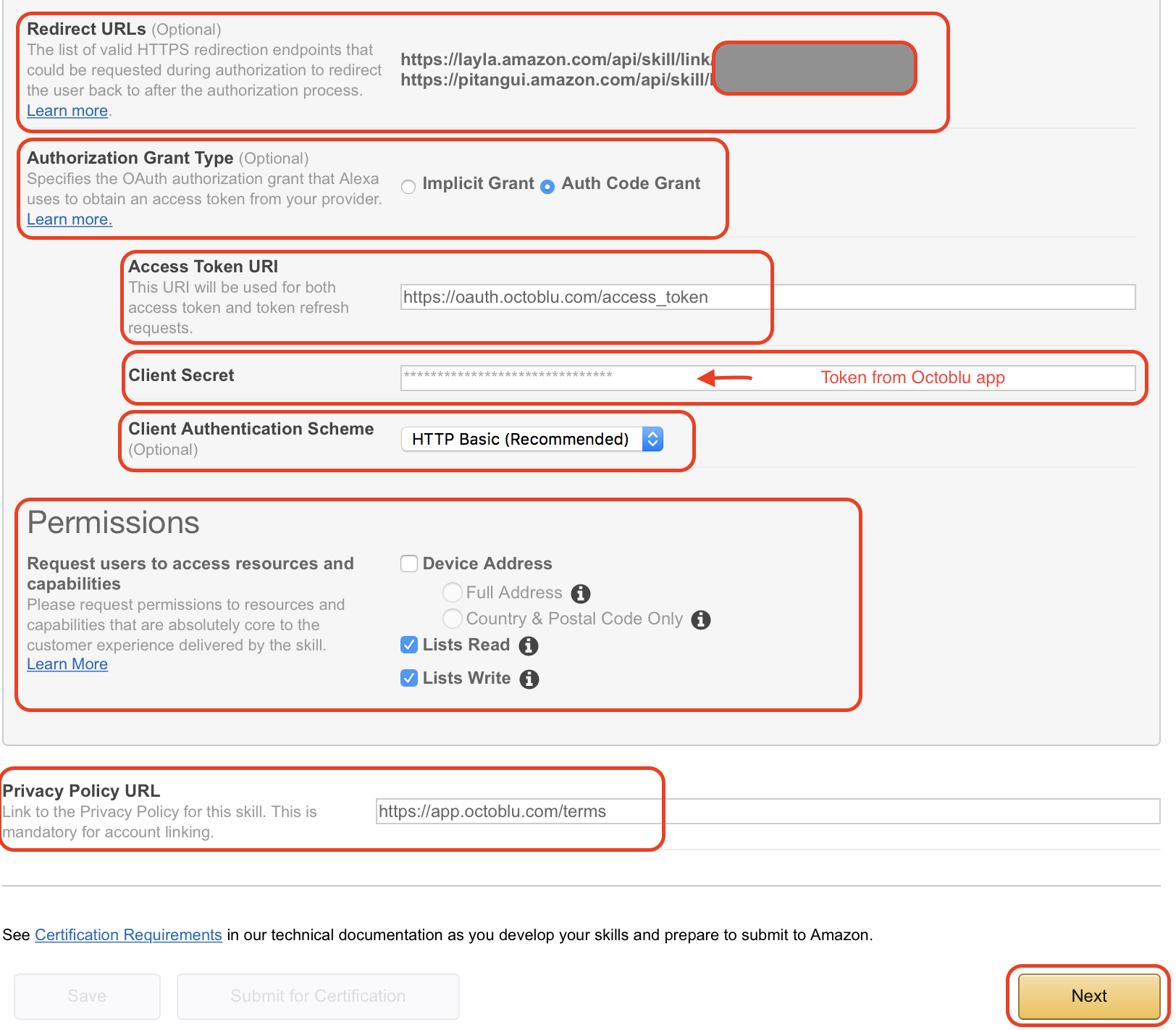 14. For the SSL certificate setup mark the “My development endpoint has a certificate from a trusted certificate authority” and click “Next”
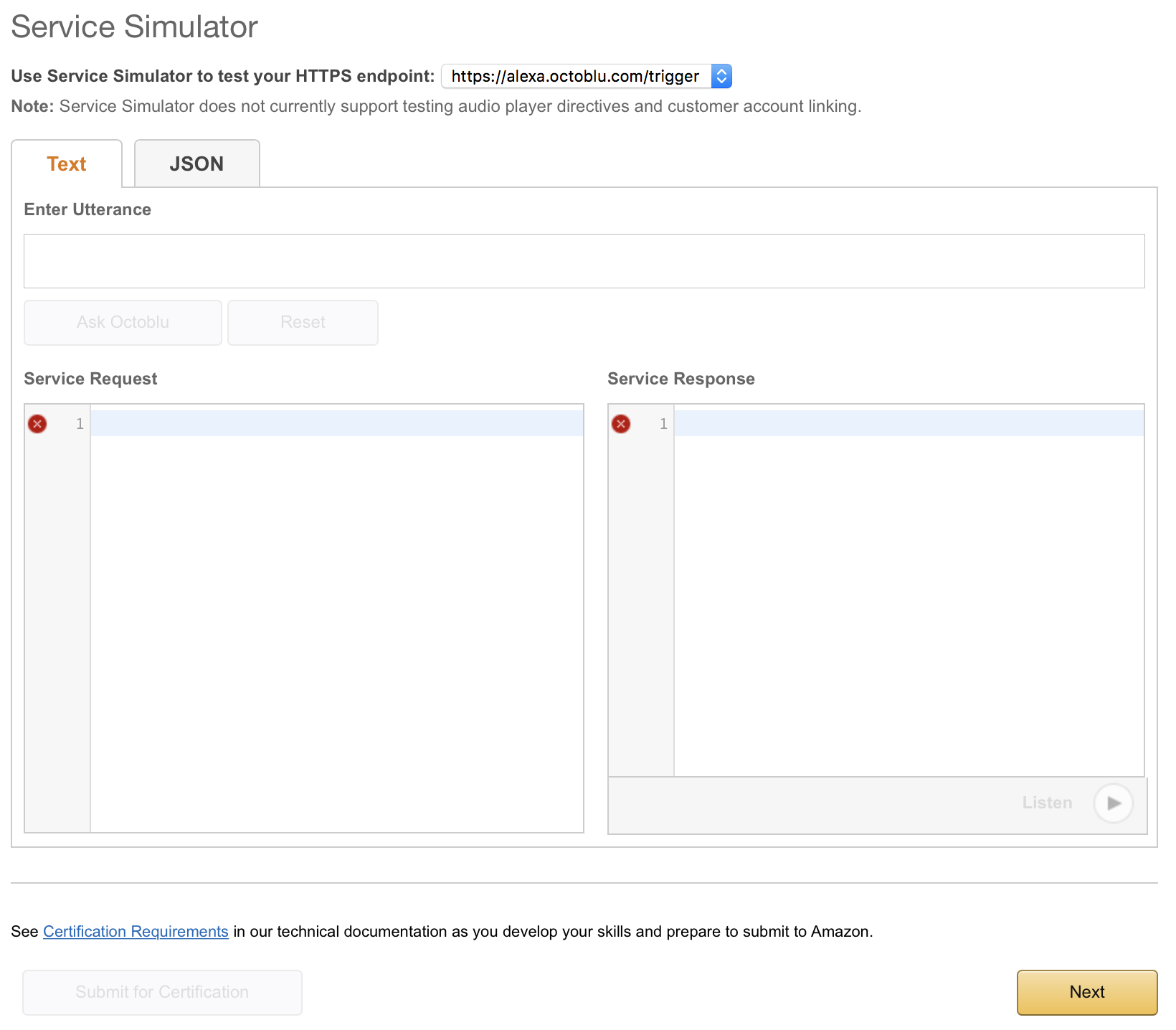
14. For the SSL certificate setup mark the “My development endpoint has a certificate from a trusted certificate authority” and click “Next”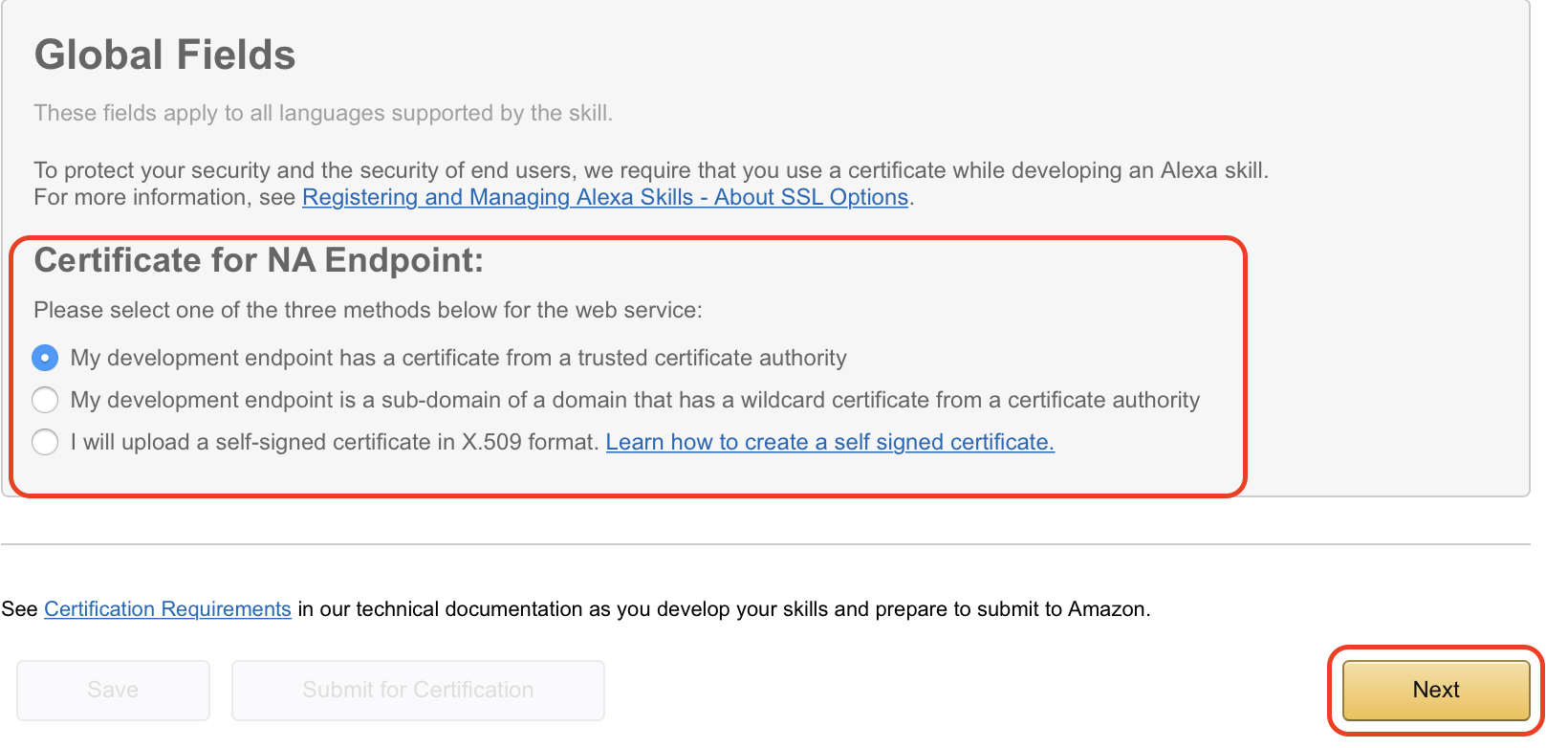 15. The next page isn’t used in my case, but just so you can follow along this is what it looks like. Click on “Next” to continue.
15. The next page isn’t used in my case, but just so you can follow along this is what it looks like. Click on “Next” to continue.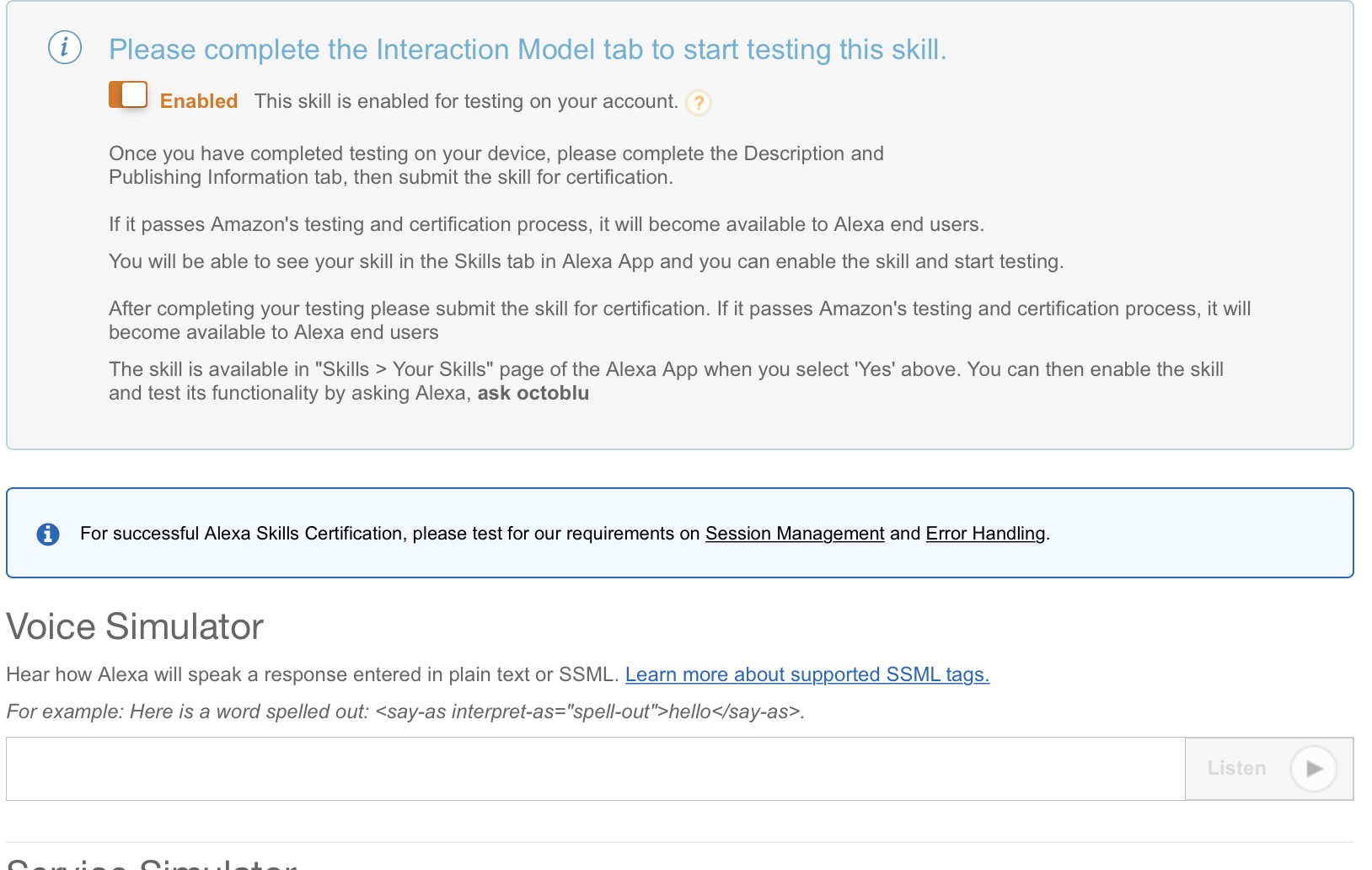
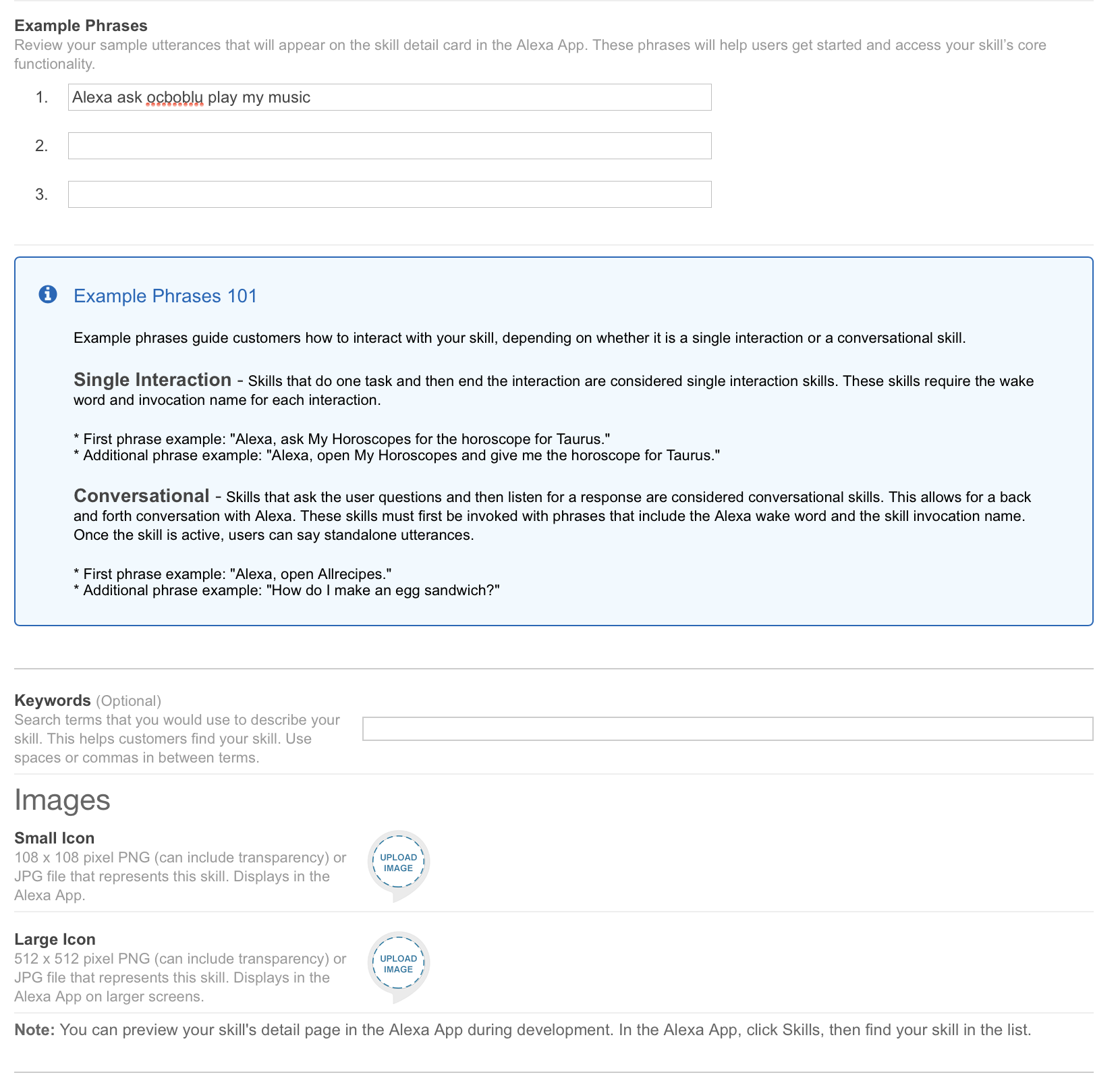
 16. The publishing section isn’t used in my case either. I did put a bit of information in there and I have posted screenshots below so you can follow along. Click on “Next” to continue.
16. The publishing section isn’t used in my case either. I did put a bit of information in there and I have posted screenshots below so you can follow along. Click on “Next” to continue.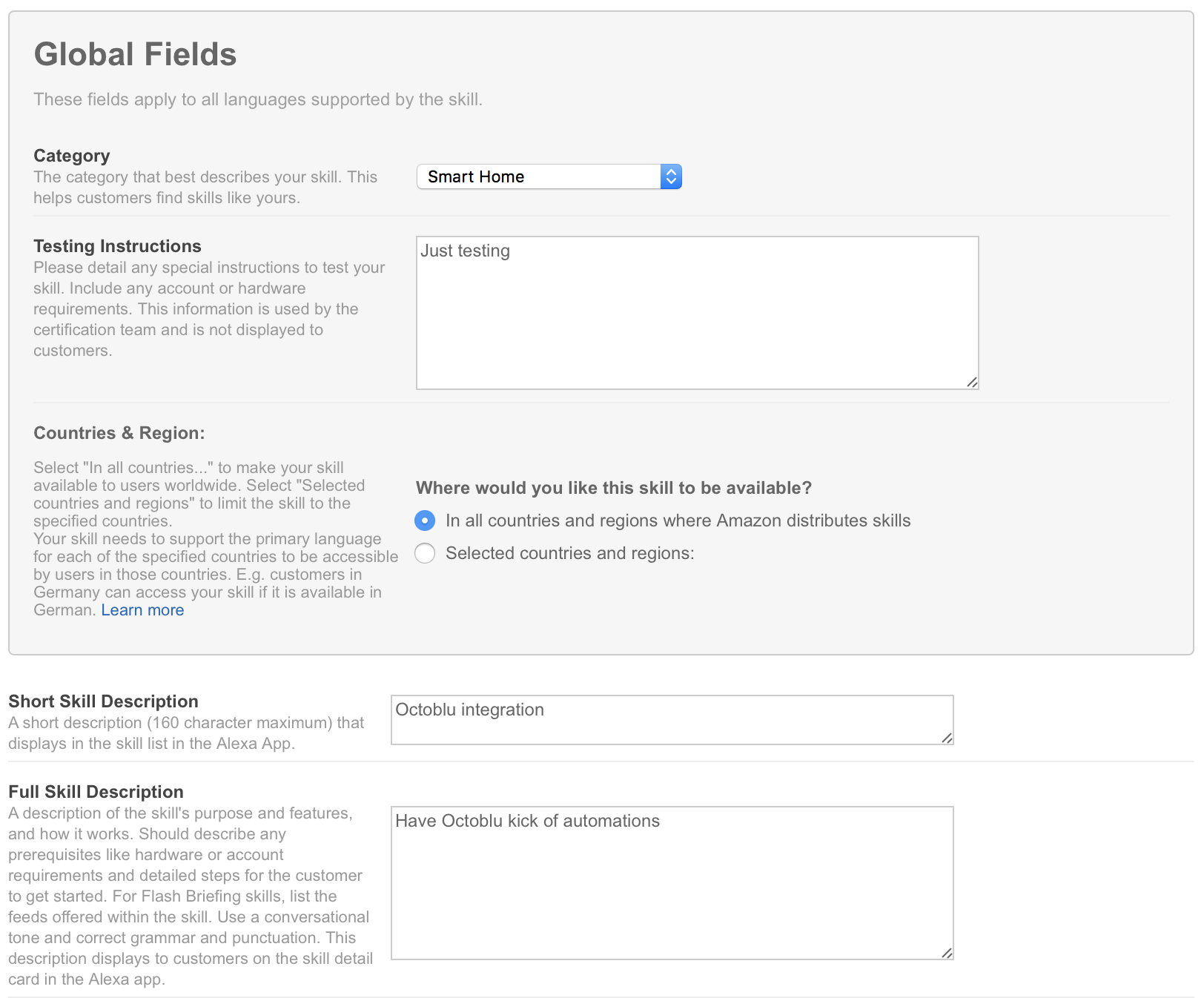
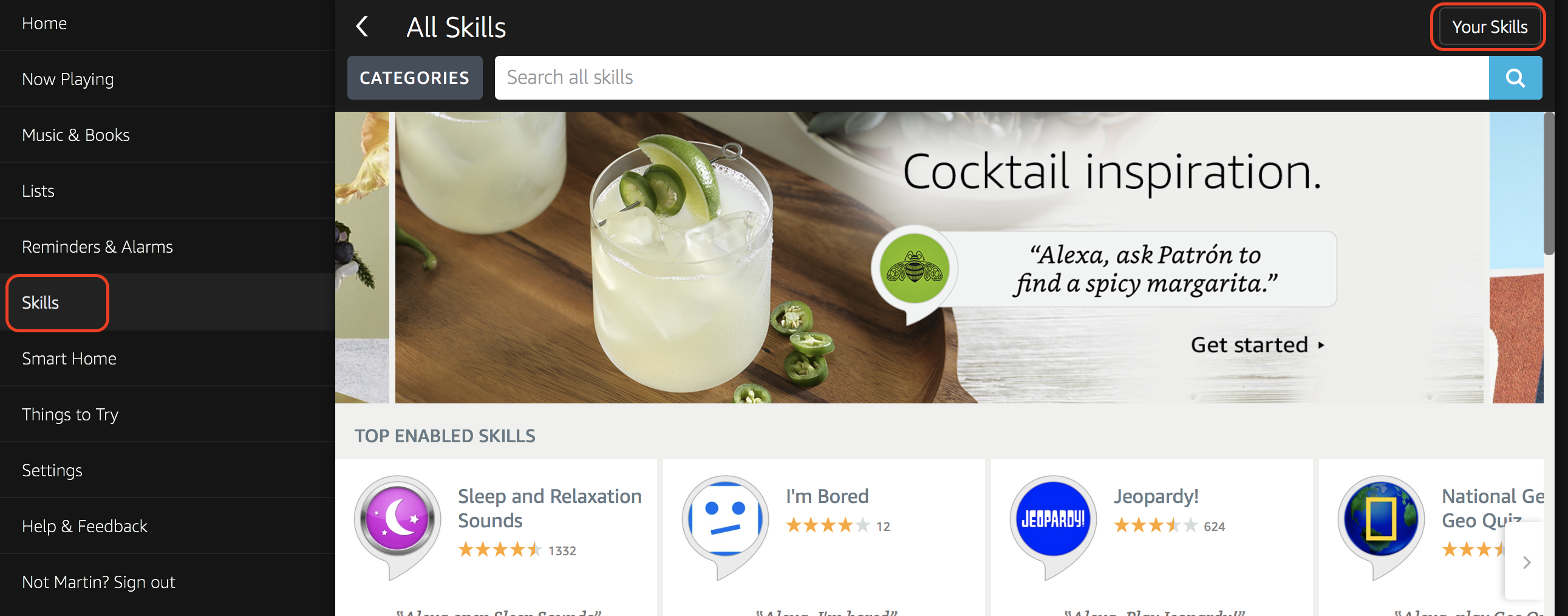
 17. On the last tab, we have privacy settings. I have filled them out, but since I am not publishing this skill it really isn’t needed. Click on “Save” to complete the setup.
17. On the last tab, we have privacy settings. I have filled them out, but since I am not publishing this skill it really isn’t needed. Click on “Save” to complete the setup.